
Crypto storage, custody and security
You might have heard the mantra: Not your Keys, Not your Crypto. If you are new to the world of crypto, this might not be intuitive, but this mantra is fundamental for many crypto investors. But what does it really mean? How can you safely store, secure and own your crypto? We'll dive into that and more in this article. Let's kick it off with...
Crypto storage options
Ok, let's set the record straight: "crypto storage" is actually a misnomer. Your crypto coins and tokens are always stored on the blockchain. They are not stored in your exchange account, or in your crypto wallet. But to make withdrawals and transfers, you need something called a private key to sign transactions, proving you are the owner. This is the "not your keys" part of that mantra.
If you don't possess the private key, then you don't have custody of (or guaranteed access to) your crypto. So this section should really be called Crypto Custody Options. But there's a lot of confusion about how crypto actually works, so this is a great thing to clear up before diving deeper.
So what the heck is a private key?
In very practical terms: the private key is the only thing that can sign transactions on the blockchain. Whoever has the private key has custody. It's kind of like the keys to your house.
For the geeks reading this: blockchains use something called Public-Key Cryptography (PKC) to validate the authenticity of something (i.e. crypto ownership) by using asymmetric encryption. PKC uses trapdoor functions: algorithmic puzzles that are easy to solve in one direction (using the private key), but nearly impossible to solve in the other direction (using the public key).
But what is the private key, really? It is an extremely long number, something that would be impossible to guess. It would take thousands of years for super computers to reverse engineer or guess the address. Pick a number between 1 and 2256. That's a private key.
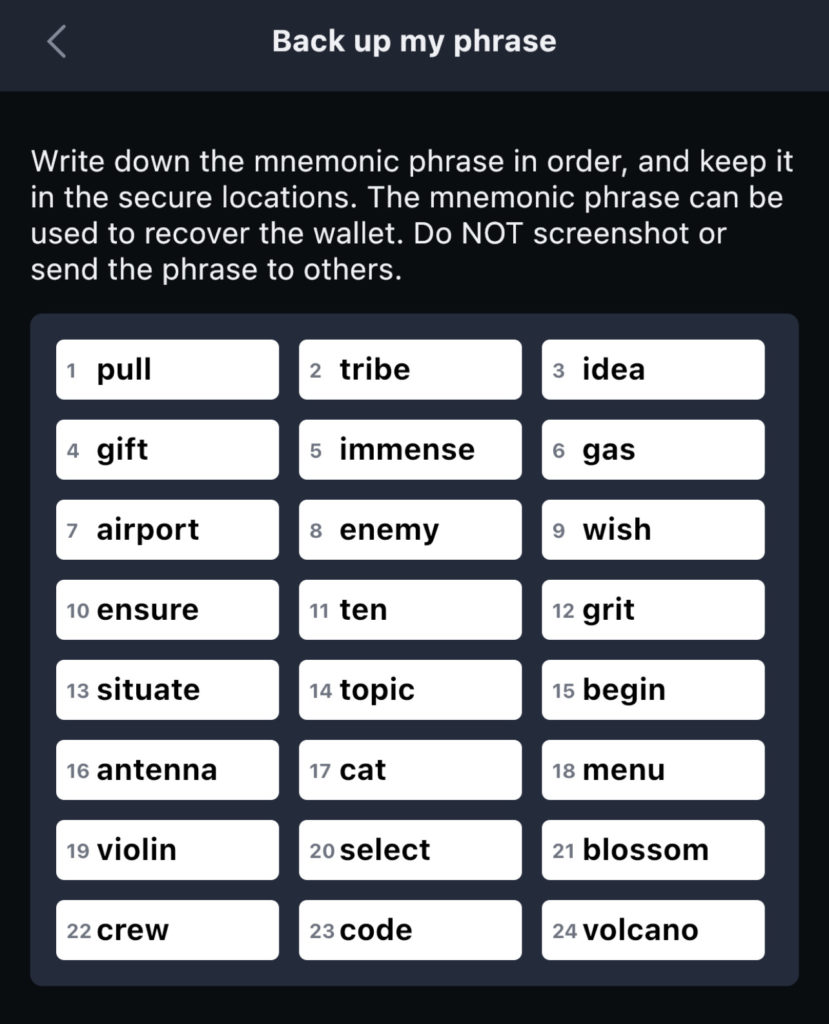
Your wallet will generate sets of Private and Public keys, which are derived from your wallet's unique Seed. The Seed can be generated using various methods, but mnemonic phrases are the most common method employed today for the average user.
Methods to Generate Cryptographic Seeds
- Mnemonic Phrases
- Typically 12 or 24 random words which are encrypted to make the very long number
- 64 digit hexadecimal code
- 256 character binary code
- Base64 encoded string
- WIF String
To summarize how these keys are all derived: Seed Phrase 👉 Private Key 👉 Public Key 👉 Crypto Address
Crypto Custody Options
Ok, now that you understand the basics of seed phrases, private/public keys and where crypto is actually stored, let's talk about custody. You've got two options: trust a 3rd party, or create a private wallet.
3rd Party Custody
For most people, 3rd parties include crypto exchanges and crypto banks. Let's use the Kraken exchange as an example, but this applies to any 3rd party. You could create an account with Kraken, fund the account and start buying crypto. Under no circumstances do you have access to the private key. They are the custodian, and you are trusting them with your crypto. Kraken is an excellent, trustworthy and reputable exchange, so in general, this is fine. But it's not risk-free, and trust is the critical factor for choosing a 3rd party.
Risks of using a 3rd party include:
- Hackers compromising the system and stealing crypto from account holders
- Service interruptions: you might need access to your funds, but the exchange is down/unavailable/etc.
- Governments could freeze your account and seize your funds
Benefits of using a 3rd party include:
- Quick access to buying and selling crypto, with advanced trading options
- Access to investment tools, like interest bearing accounts, crypto staking and crypto lending
- Security is handled by the 3rd party, offloading the task from you (at the expense of trust)
Private Crypto Wallets
Private wallets come in many forms: iOS and Android apps, desktop apps and Chrome browser extensions. And you can also buy hardware wallets, like Ledger, Trezor and SafePal.
With a private crypto wallet, you own the private key, so you always have custody. You can always access your crypto and do as you please. This is a liberating thing! But with great power comes great responsibility. Private wallets are more complicated to operate, more prone to human error, and they carry a different set of risks. It's critical that you educate yourself.
Security protocols for private wallets is a much deeper topic than this article can go, but here are the most important security pointers:
- NEVER EVER give your seed phrase or private key to anyone
- NEVER EVER store your seed phrase or private key on a computer
- Read 1 and 2 ten more times, and never forget them!
- Store your seed phrase offline, in a safe place, on a secure medium (like steel or titanium)
- See our crypto seed storage guide for more details, and storage strategies
Seriously, there are many crypto fortunes that have been forever lost due to seed phrases and private keys getting compromised. The most common attack vectors are hackers using malware, key loggers, viruses and phishing schemes. But physical attacks can happen too.
While the vast majority of people are safe using private wallets, you don't want to be the person who got hacked, fell for a scam and lost a chunk of their portfolio.
Risks of using a private wallet include:
- Private keys getting compromised and funds being stolen
- Phishing schemes and scammers tricking you into transferring funds
- Physical attacks
Benefits of using a private wallet include:
- Your keys, your crypto!
- Generally better access to crypto staking, which can earn high APY rewards
- Access to the entire world of crypto and DeFi (Decentralized Finance)
- While centralized exchanges like Binance can offer a wide variety of tokens, private wallets give you access to DeFi, new projects, IDO's, DAO's and so much more
- Often times, private wallets are required to get in early on new crypto projects
If you want to create a private wallet, you can use software to create a hot wallet, or use hardware to create a cold wallet. You might be wondering whats the difference is between a hot wallet and a cold wallet. You can read all about it in our other article, but here is the TL;DR:
- Hot wallets use software on your desktop or mobile phone to create the private key
- They are considered "Hot" because the private keys are stored on a device that is always connected to the internet
- Hot wallets are free, easy to make and convenient to use
- Hot wallets use passwords, pins, fingerprints or FaceID to authorize transactions
- Examples of hot wallets include MetaMask, Trust Wallet and Terra Station
- Cold wallets use physical hardware to safely generate and secure the private key
- Hardware wallets are never connected to the internet
- Hardware wallets require physical authorization to approve transactions on the device
- Cold wallets are the most secure option
- You must purchase hardware wallet to use it. Examples include Ledger, Trezor and SafePal
Wrapping up
As you can see, crypto custody is a pretty deep topic. And for most people, they will use multiple custody options to help maximize access to different crypto currencies, investment options and diversify their risk. After all, having all your crypto in a single wallet would be like putting all your eggs in one basket.